Researchers:
Statement from Slack
Slack would like to thank the researchers for their work to increase the security of the open source tool LibreOffice and their responsible disclosure to Slack. The security of file sharing is critically important to Slack and its users, and we worked with the research team to quickly implement a fix within 24 hours of receiving the report. Slack has confirmed that no customer data was accessed using this bug.
Intro
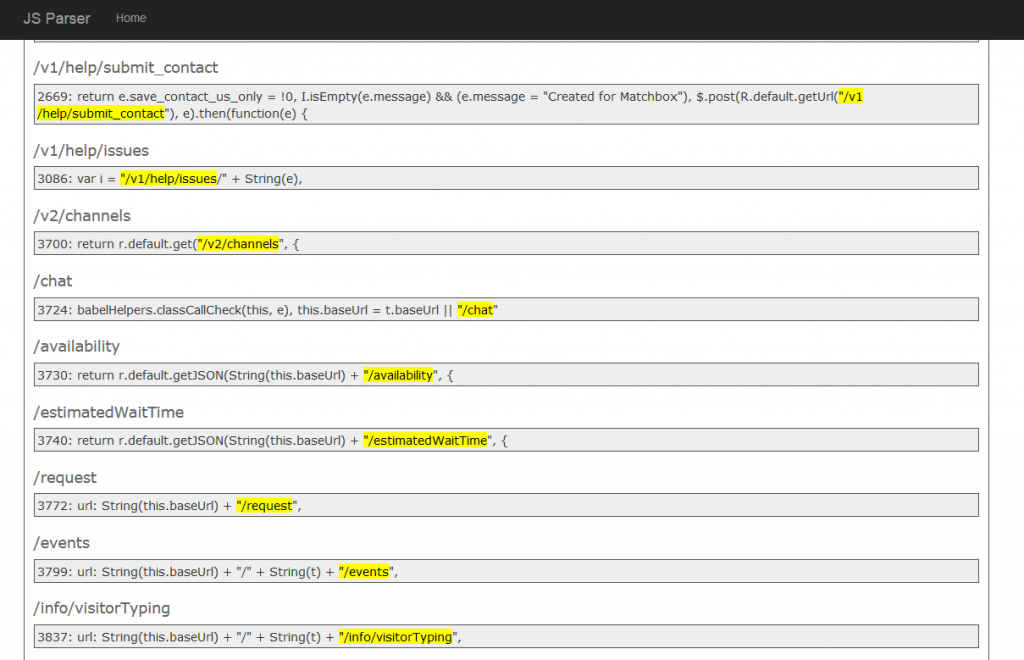
In our attempt to fingerprint LibreOffice as a PDF rendering service, we identified multiple implementation vulnerabilities.
This writeup covers our efforts to fingerprint LibreOffice, LibreOffice file detection (and abuse) & misuse of the LibreOffice Python-UNO bridge.
The unintended misuse of the Python-UNO bridge by the popular package unoconv resulted in CVE-2019-17400.
We believe our research here is not final, and encourage others to look into this area.